5 Cybersecurity Risks Your Business Might Be Missing
Outline:
– The Hidden Gaps: Where modern businesses overlook risk
– Practical Protection: Turning policy into everyday behavior and controls
– Choosing Your Stack: Comparing security capabilities and trade-offs
– Habits and Quick Wins: Small moves that compound over time
– Summary for Business Leaders: Assessment and a focused action plan
Introduction
The modern company runs on a dense web of laptops, routers, sensors, cloud services, and line‑of‑business apps. That interconnected stack drives speed and margin, yet it also multiplies the places where a single misstep can ripple into downtime or data loss. The key is to treat cybersecurity as an operating discipline, not an IT add‑on. With the right mix of technology, process, and habits, you can lower risk while still shipping features, serving customers, and meeting growth targets.
Section 1 — The Hidden Gaps: Where Risk Enters Quietly
Before alarms blare and dashboards light up, exposure usually starts with routine oversights. Think of default passwords never changed on a smart printer, a cloud storage bucket made public during a hurried migration, or a patch window missed because a release deadline loomed. These aren’t headline‑grabbing failures, yet they add up. To ground the conversation, consider the common cybersecurity vulnerabilities businesses face today: phishing that steals credentials, weak or recycled passwords, misconfigurations in cloud and network gear, unpatched software and firmware, and shadow IT purchases that silently expand the attack surface.
Studies consistently show that people and process weaknesses are involved in a large share of incidents. A single convincing email can prompt an employee to authorize a fake payment or grant a malicious app broad permissions. Meanwhile, many exploited flaws are not zero‑day mysteries; they are known issues left unaddressed for months. Average detection times still hover in the many‑month range across industries, giving intruders room to move laterally, escalate privileges, and exfiltrate data. On the hardware side, overlooked firmware updates for laptops, storage arrays, and network switches can leave reliable workhorses with very avoidable holes.
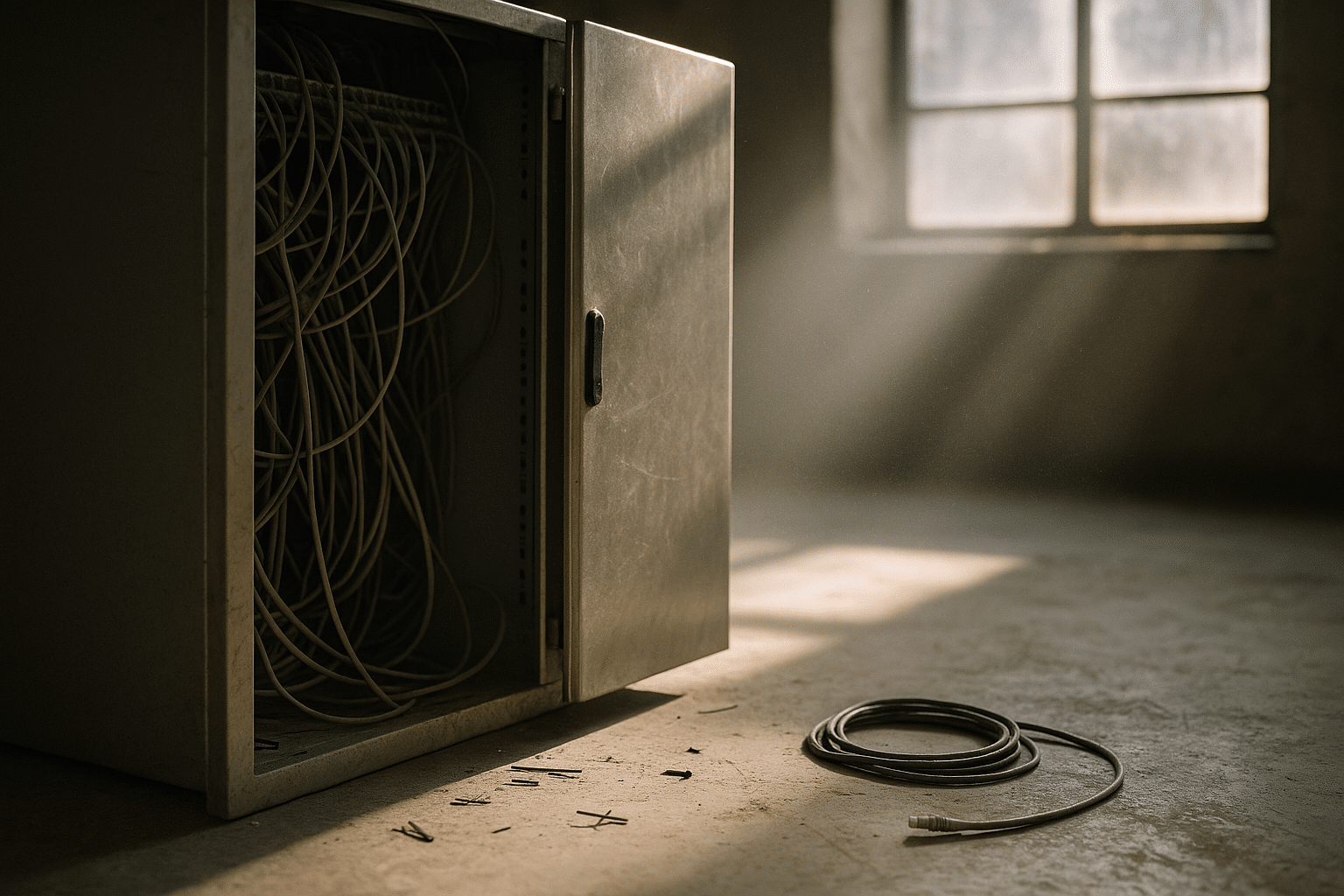
What makes these gaps uniquely risky is their compound effect. Cloud misconfiguration plus credential reuse plus delayed patching is a recipe for trouble even without a highly resourced adversary. Small details in computers & electronics matter: USB autorun policies, BIOS protections, secure boot, and disabling unused ports can remove easy paths in. Consider the supply chain, too. A trusted plug‑in or vendor account can become an indirect doorway if least‑privilege is ignored. Map these realities to business outcomes and it’s clear: resilience depends less on exotic tools and more on closing everyday doors.
Section 2 — Practical Protection: Turning Policy into Everyday Behavior
Once you recognize the entry points, the next step is turning intent into practice. Leaders often ask for actionable ways to protect company data from online threats, and the answer blends governance with controls that fit the flow of work. Start with identity: require strong authentication for all users, especially admins, and restrict high‑risk actions with step‑up verification. Pair that with least‑privilege access so employees use the rights they need and nothing more. Encrypt data in transit and at rest, and classify sensitive information so protection follows the asset, not just the location.
Endpoint discipline is non‑negotiable. Laptops, tablets, and phones should run managed configurations with disk encryption, automatic updates, and hardened settings. Email and collaboration tools need phishing and malware filtering that checks links and attachments before they reach the inbox. Network segmentation reduces blast radius: finance systems, lab devices, and guest traffic should not mingle. Backups must be frequent, offline or immutable, and tested; a backup that can be encrypted or deleted by attackers is hardly a backup at all. Because many attacks rely on speed and confusion, well‑rehearsed incident playbooks help teams act decisively instead of improvising under pressure.
To make protection stick, integrate it with day‑to‑day operations and training. Short, role‑based refreshers beat yearly marathons. Tie security checks to release pipelines and device onboarding so they happen automatically. When possible, select tools that reduce clicks and friction; controls that are painful get bypassed. Practical priorities include:
– Enforce multifactor authentication for every external access point and admin session.
– Standardize secure baselines for operating systems, browsers, and firmware.
– Apply critical patches on a defined cadence, with emergency paths for high‑severity fixes.
– Use logging that preserves integrity so investigations can trust the data.
None of this requires stalling the business. The goal is to align guardrails with how teams build, sell, and support, so safety becomes routine rather than a special event. When protective measures are embedded and measured, risk drops quietly, just as it once rose.
Section 3 — Choosing Your Stack: Capabilities, Trade‑offs, and Fit
Tool sprawl is real. Many organizations accumulate overlapping platforms for endpoints, email, network filtering, and cloud visibility, yet gaps persist because the pieces don’t align with use cases or staff capacity. It helps to review available security options for your organization through the lens of capability and operations, not just features. For endpoints, modern detection and response tools go beyond signature checking to analyze behavior, isolate hosts, and roll back changes. That extra capability can be the difference between containing one infected laptop and scrambling across an entire fleet.
For visibility, centralized log collection and analytics can correlate signals from devices, servers, and cloud services to spot patterns that single tools miss. However, analytics without people and playbooks often devolves into alert fatigue. Many mid‑size teams succeed with managed services that watch telemetry and handle first‑response, trading some control for consistent coverage. On access, there is a shift from broad, always‑on connectivity to context‑aware gateways that grant specific application access based on device health and user risk. That approach can tighten security and improve user experience compared to legacy, network‑wide tunnels.
Email and web controls are still front‑line defenses, inspecting links at click time and blocking drive‑by downloads. Data loss controls can tag sensitive content and prevent it from leaving approved channels. Password managers and single sign‑on reduce password sprawl and make strong, unique credentials realistic. Hardware security keys can harden critical accounts against phishing‑resistant attacks. When comparing these options, weigh:
– Risk reduction per dollar and per hour of team effort.
– Fit with existing device management and cloud platforms.
– How well the tool automates routine tasks and supports response.
– Reporting that maps to executive and audit needs without heavy manual work.
Finally, prefer systems that integrate via standard logs and APIs so you can stitch together a coherent view. A smaller, well‑connected set of tools that your team can operate reliably often outperforms a sprawling catalog that nobody fully owns.
Section 4 — Habits and Quick Wins: Security That Compounds
Big programs rest on simple behaviors repeated consistently. That’s good news for busy teams because there are simple steps to strengthen digital defenses that require discipline more than dollars. Start with an opinionated patch schedule: operating systems weekly for critical fixes, browsers and plugins as they release, firmware quarterly or when advisories drop. Limit administrator rights, separating everyday accounts from privileged ones. Turn off autorun for removable media and restrict unknown USB devices that can deliver malware faster than an email ever could.
On the human side, embed quick, targeted training into normal flows. A monthly, two‑minute “security moment” at the start of team meetings beats a dense slide deck. Simulate phishing with teachable feedback, not blame. Publish a simple path for reporting suspicious activity and celebrate catches to create the norm you want. For physical spaces, secure laptops with cable locks in shared areas, and keep network closets closed; a stray device on an open port can bypass many expensive controls.
Document a lightweight, repeatable routine:
– Monday: review high‑severity advisories for your operating systems and major applications.
– Wednesday: verify backups completed and perform a quick restore test.
– Friday: spot‑check ten devices for patch level and disk encryption status.
– Monthly: rotate secrets for critical integrations and prune stale accounts.
– Quarterly: test disaster recovery steps for a core service and record time to restore.
Measure what you manage. Track mean time to detect and respond, phishing report rates, patch latency, and percentage of managed devices compliant with your baseline. Publish small wins—closing an exposed port, speeding containment by fifteen minutes—to build momentum. Like compound interest, small protective habits, applied across your computers & electronics fleet and cloud footprint, create a durable advantage over time.
Section 5 — Summary for Business Leaders: Assess and Improve with Purpose
Strategy needs checkpoints. If you’re deciding where to invest next quarter, start with clarity on how to assess your current cybersecurity measures. Take inventory of assets—devices, applications, data stores—and map who uses them and why. For each critical service, ask what could go wrong, how you would know, how you would stop it, and how you would recover. Score the answers on a simple scale from ad hoc to consistently tested. The output becomes a risk register tied to business processes rather than a pile of technical jargon.
Next, validate assumptions. Run tabletop exercises for realistic scenarios: credential theft on a sales laptop, accidental exposure of a cloud dataset, or ransomware on a shared file server. Time each step: detection, triage, containment, communication, and recovery. The numbers will spotlight constraints—maybe logging exists but nobody watches it after hours, or backups are frequent yet restores take too long. Align investments to remove the bottlenecks that slow response or allow silent failure.
Translate findings into a 30/60/90‑day roadmap anchored to outcomes:
– 30 days: close high‑severity misconfigurations, enforce multifactor authentication everywhere, and verify offline or immutable backups.
– 60 days: standardize and deploy secure device baselines across laptops and servers; segment one high‑value environment to reduce blast radius.
– 90 days: integrate centralized logging with alerting and on‑call process; run a full recovery test for a core application and document results.
Finally, report progress in business terms: reduced likelihood of payment fraud, faster customer portal recovery time, fewer hours spent on avoidable outages. That is the language that sustains funding and focus. Cybersecurity is not a finish line; it is a management system for uncertainty that protects revenue, reputation, and the people who rely on your services. With steady assessment and targeted improvements, your organization can stay agile without leaving the door open.